Four Tips to Combat Compromised Credentials
Contributing Author Brett Williams , APAC Solutions Architect, Flashpoint discusses the key steps needed to protect against a compromised credential breach.
In many cases, passwords are the primary line of defence protecting user accounts from being hijacked in an account takeover (ATO) attack. With the right policies and parameters in place to ensure strong, unique passwords, this defence can be quite effective. That being said, as we all know, passwords are highly susceptible to human fallibility.
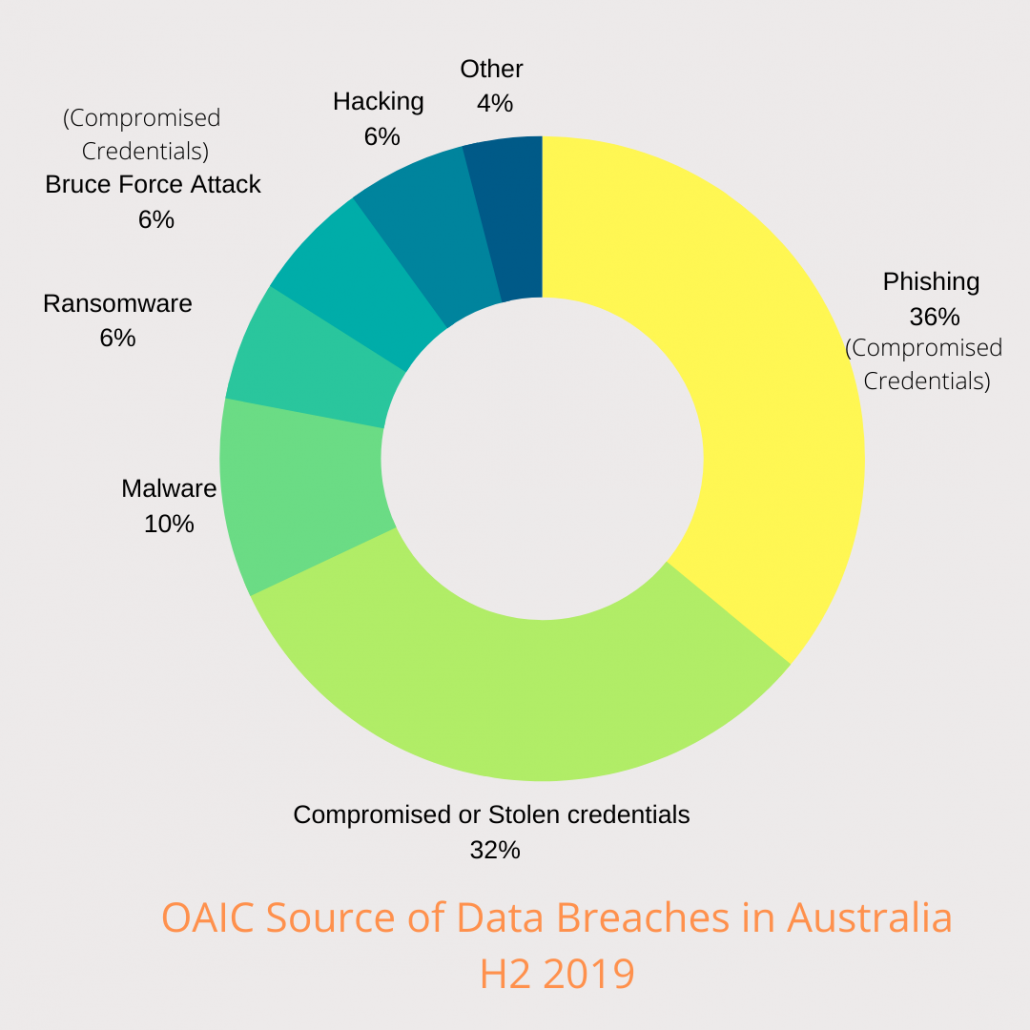
In the latest Notifiable Data Breach report (covering breaches in Australia for the last half of 2019)* issued by the Office of the Australian Information Commissioner (OAIC), it was found that 68% of breaches were related to compromised credentials. Of which 36% of the credentials were obtained by phishing and 32% were from other methods. These methods could include credential-stealing malware and compromised databases/websites.
In addition, there is an overlap between personal and work-related account passwords. With the rise of credential stuffing, adversaries can take a set of username/password combinations obtained by attacking one target and use them to compromise employee or customer accounts with other organizations. Easier yet, threat actors can even carry out credential stuffing using the low-hanging fruit of publicly disclosed dumps available on the open web.
Such activity can pose a business risk on several fronts—from the financial and reputational costs of fraud against customer accounts to the potentially massive impact of adversaries gaining privileged network access through ATO against an employee account.
More recently, the COVID-19 pandemic continues to be reflected in cybercriminal activities. Malicious actors are taking advantage of global fear and uncertainty and exploiting them through attack vectors that include tailored phishing lures and custom malware. For instance, continuous and long-term working from home can create a sense of isolation in employees, which in turn can lead to low morale. This environment (combined with the anxiety introduced by the COVID-19 pandemic) can increase individuals’ susceptibility to malicious social engineering attempts to collect credentials to be used in attack campaigns against corporate remote access infrastructure. For many organisations, usernames and passwords are their only line of defence into remote access to critical enterprise systems.
With the surge in remote working, video conferencing solutions, such as Zoom, has seen a sharp increase in usage., In April 2020, reports surfaced that over 500,000 Zoom accounts* were sold across the dark web marketplaces likely for use in “zoombombing” or other malicious activities. These credentials were likely obtained as a result of credential stuffing attacks.
In the ecosystem related to credential stuffing operations, it is very common for threat actors performing the account checking to leverage combo lists (aggregated lists of previously leaked credentials) containing millions of potential credential pairs (email: password) to create a validated list of accounts. This technique can then be used for fraud activities and to launch attacks against websites and applications.
As the technology and tools to leverage stolen credentials advance, a more thoughtful approach to your organization’s password policy is a highly effective way to reduce risk by better protecting your customers, network assets, and employees. While there’s no one-size-fits-all approach to optimizing password policy, the following four measures and best practices are worth considering:
- Monitor for Compromised Credentials – Dumps containing compromised passwords, usernames, and other credentials are easy pickings for threat actors, and employee or customer accounts using these credentials are ripe for the taking. By monitoring public dumps and leaks privately shared and sold only within illicit online communities, defenders can assess the exposure of accounts they’re tasked with safeguarding and take proactive action against ATO.
While establishing the data collections and technology required to automatically monitor, process, and act upon compromised credentials data is extremely talent and resource-intensive, organizations can gain these capabilities through a trusted partner. In doing so, defenders can augment traditional password policy best practices with the ability to take action based on indicators observed within the cybercrime underground.
- Use a Password Manager – While in many circles it’s become conventional wisdom, it bears repeating: password managers are an easy, efficient way for users to maintain unique passwords for each account. That being said, a word of caution is in order: not all password managers are created equal, and using a password manager that is insecure or unreliable can lead to all of a user’s passwords being lost or compromised at once.
- Know When to Reset Passwords – While long accepted as a best practice, cybersecurity leaders are increasingly coming around to the realization that automatically forcing password resets at a specified time interval—such as every 90 days—does not reduce the likelihood of accounts being compromised. On the contrary, forcing users to frequently come up with new passwords can encourage them to reuse a password they’re already using for another account or simply make a slight modification to an existing password. The most effective policy is to only reset passwords known to have been exposed in breaches, which can be accomplished by monitoring for compromised credentials and simultaneously make users comfortable with using complex passwords or phrases.
- Enforce Complexity and Uniqueness Standards – Case-sensitive combinations of letters mixed with special characters are exponentially more difficult for automated brute-forcing tools to mathematically guess than simple combinations of words and numbers—and the longer the password the better. And while it’s unlikely that users will be able to memorize lengthier, more random credentials, adopting the aforementioned best practice of using a password manager makes it easy to implement and enforce strict standards for complexity and uniqueness.
While these best practices are not a comprehensive roadmap to strong password hygiene, they’re a great starting point for organizations that have taken laissez-faire or reactive stance when it comes to ensuring the security of user credentials. In particular, as the technology and tools to leverage stolen credentials advance, defenders should seek out innovative new ways to proactively flag exposed passwords leveraging insights gleaned from illicit communities and open-web dumps.
*https://www.oaic.gov.au/privacy/notifiable-data-breaches/notifiable-data-breaches-statistics/
*https://www.bleepingcomputer[.]com/news/security/over-500-000-zoom-accounts-sold-on-hacker-forums-the-dark-web/
To Learn more about Flashpoint and Compromised Credential Monitoring: Click Here
————————————————————————————————————————
Brett Williams Bio (https://www.linkedin.com/in/brettwilliams/):
As Lead Solutions Architect at Flashpoint, Brett works with clients to help them use intelligence within their enterprises and how deep and dark web monitoring should be an integral part of any threat intelligence program. He is responsible for providing relevant intelligence and services to address various use cases including, insider threat, cyber intelligence, anti-fraud, physical security and counter-terrorism. Brett is widely recognized for his extensive and in-depth knowledge of the security landscape. He has experience working across industry sectors including finance, government, law enforcement, healthcare and education. He has over 28 years’ experience working in information technology and security with a focus on incident response, intelligence, security operations and digital forensics.

